this will actually work. From the very beginning, we have never had a random number generator that mathematicians could not somehow reverse engineer. At best we have made it just too expensive.
Understand that this issue actually defeated Gertmany in WWII. It is sort of important and why a truly working random number generator is so sought after.
so if we can physically do this, it is good.
Cosmic-ray muons used to createysically cryptography system
16 Jan 2023
https://physicsworld.com/a/cosmic-ray-muons-used-to-create-cryptography-system/
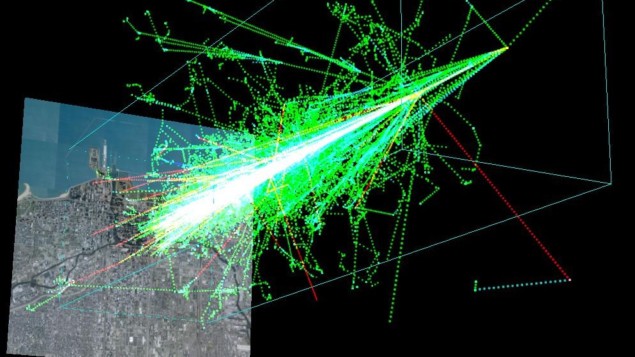
Cosmic rain: Simulation of a particle shower created by a 1 TeV proton hitting the atmosphere 20 km above the Earth. (Courtesy: Dinoj/CC BY 2.5)
The random arrival times of cosmic-ray muons at the Earth’s surface can be used to encode and decode confidential messages – according to Hiroyuki Tanaka at the University of Tokyo. He claims that the new scheme is more secure than other cryptographic systems because it does not require the sender and receiver of a message to exchange a secret key. Having confirmed important aspects of the technology in the lab, he reckons it will be commercially competitive for use over short distances in offices, data centres and private homes.
Cryptographic protocols involve generating and distributing a secret key that is used to encrypt and decrypt messages. Today, commonly used cryptography systems could be cracked by those with the ability to find the prime factors of very large numbers. This is fiendishly difficult to do using conventional computers but it should be a much easier task using quantum computers of the future.
Among the options for dealing with this threat is itself quantum – the use of Heisenberg’s uncertainty principle to ensure that any would-be eavesdropper cannot steal the key without revealing their presence in the process.
Quantum flaws
However, even this “quantum key distribution” has its flaws. Scientists have shown it is possible to exploit weaknesses in the encryption hardware, such as shining bright light on single-photon detectors to turn them into classical devices. This particular problem can be avoided by using a third party (who need not be trustworthy) to carry out the detection of key bits, but this arrangement is more expensive than straightforward two-party encryption.
Tanaka’s new proposal is designed to defeat eavesdroppers by instead turning to a natural and ever-present resource of randomness: cosmic-ray muons. Cosmic rays, which are mainly protons, rain down on the Earth from deep space and generate showers of pions and other particles when they collide with nuclei in the atmosphere. Those pions then decay into muons, which are heavy versions of the electron. These muons hit the Earth’s surface completely independently of one another and are able to pass through large amounts of solid material while only losing a small fraction of their energy by ionizing the materials.
The idea is to position the message sender and receiver close enough to one another that they are both exposed to the same cosmic-ray showers and can make their own separate detections of specific muons within a shower – namely, those particles whose trajectory crosses the detectors of both individuals. By each recording the arrival time of those muons and using the time stamps as the random data for cryptographic keys, the sender and receiver can independently generate the same secret keys – without having to send the keys to one another.
Synchronized clocks
Ensuring that sender and receiver use the same muons to create the keys relies on working out the precise time delay between the two detections, which is done by knowing the distance between the detectors (muons typically travel at 99.95% of light speed) while carefully synchronizing clocks at each end. Synchronization can be achieved using a global-positioning system to coordinate the ticking of local clocks such as crystal oscillators.
Tanaka calls his technique “Cosmic Coding & Transfer” (COSMOCAT) and it uses two detectors that measure muon arrival with a plastic scintillator and a photomultiplier tube. Carrying out tests on four different days in June last year, he showed that muons do indeed arrive at random points in time – the probability of observing a given number of events in a certain period following a Poissonian distribution. He also showed that the two detectors consistently produced the same, random time stamps.
However, owing to limitations in the GPS signals and the electronics used to carry out the experiment he was only able to establish common muon detections (as opposed to interception of other random particles) in about 20% of cases. Overcoming this problem involved the receiver using multiple keys to try and decode a given message and then moving on to the next message only once the receiver had signalled success.
Smart buildings
These extra steps add time to the decryption process and so slow down the rate at which data can be transmitted. Nevertheless, Tanaka says that the system would still be considerably quicker than much existing technology. Indeed, agreed detections took place at an average of around 20 Hz, implying a data transmission rate of at least 10 Mbps. This is faster than the 10 kbps that is typical of a local network system such as Bluetooth Low Energy. He reckons that this greater bandwidth should make the new scheme attractive for short-range wireless communication such as connecting sensors within “smart” buildings and securely exchanging information during the powering of future electric
Like Tanaka, Michail Maniatakos of New York University Abu Dhabi in the United Arab Emirates has worked on developing a random number generator from cosmic muons for cryptography. But he and his colleagues found that muons do not arrive at the Earth’s surface in sufficient numbers to generate enough “entropy” in a given amount of time from a suitably small detector. “Our research concluded that muons are not a practical approach for sourcing randomness in a real system,” he says.
Tanaka acknowledges that muon detection rates place limits on the technology but insists that rates are adequate for wireless communication over distances of up to about 10 m. In his demonstration he used quite large detectors – each measuring 1 m2 – in order to maximize the bit rate. However, Tanaka reckons he could shrink the detectors to a fifth of their current size by upping the key generation rate by a factor of five. As to how long it will take to perfect the technology, he says he should have a working prototype within five years.
One potential weakness in the scheme, he notes, is the possibility that an eavesdropper could position a third detector between the sender’s and receiver’s devices and record the muon strikes independently. He reckons that any such plan would be “totally impractical” but says that the system comes with a built-in safeguard – a small temporal offset compared with standard time broadcast by GPS satellites. This offset, which the communicating parties can change at any time of their choosing, causes the would-be eavesdropper to disagree on the muon arrival times – with the upshot, he says, that they “cannot steal the key to decode the message”.
No comments:
Post a Comment